Overview
Security is very important to us at Nuclei. In fact, it's so important to us that we engage a third-party firm to audit our infrastructure, systems, and processes continuously.
That firm's called Vanta, and they make a report that covers everything they check — it's almost like a pen test for our entire organization! Their reports are updated daily, and are available upon request.
Architecture
Nuclei adheres to the “Serverless Application Lens” that is part of the “AWS Well-Architected Framework” to ensure that all applications and workloads are architected according to best practices from AWS.
The "Security Pillar" of the framework includes the ability to protect information, systems, and assets while delivering business value through risk assessments and mitigation strategies.
Nuclei implements all five best practice areas for security in the cloud, including:
- Identity and access management
- Detection controls
- Infrastructure protection
- Data protection
- Incident response
Serverless architectures like Nuclei's address some of today’s biggest security concerns as it removes infrastructure management tasks, such as operating system patching, updating binaries, etc.
Serverless
Nuclei's end-to-end application architecture is serverless. This in turn completely eliminates the largest risk surfaces that exist in traditional applications from the beginning.
Under the "Shared Responsibility Model" for security in the cloud, responsibility for the most vulnerable parts of any infrastructure (OS configuration of compute instances, network access, firewall configuration, etc.) shift from the application provider to AWS (which runs the tightest DevOps in the world).
Real-time vs. historical compliance practices
We've built end-to-end automation enabling direct, real-time inspection of Nuclei's information security compliance directly into our infrastructure (AWS), our code, and our organization (HR platform, productivity tools, security training platforms, background check processes, etc.)
This in turn enables our customers to view reporting on Nuclei's real-time compliance posture at any moment in time.
This differs significantly from the approach other providers take, which is focused on:
- Historical compliance at some point in time in the past
- Future checkpoints to ensure nothing has slipped
- A "trust us" promise not to fall out of compliance in the interim.
Frequently Asked Questions
Which security features of AWS are being used?
In general, we adhere to the “Serverless Application Lens” that is part of the “AWS Well-Architected Framework” to ensure that all applications and workloads are architected according to best practices from AWS. (which includes the “Security Pillar”)
Nuclei's complete technology stack is “serverless”, which eliminates some of the largest security concerns from the beginning:
Traditional AWS Application
With a traditional application, the security of the Platform, OS, network, and data (at rest and in transit) remains the responsibility of the application provider or the end customer. : 
Serverless AWS Application
With a serverless application, the security of the Platform, OS, network, and data (at rest and in transit) shifts to the infrastructure provider:
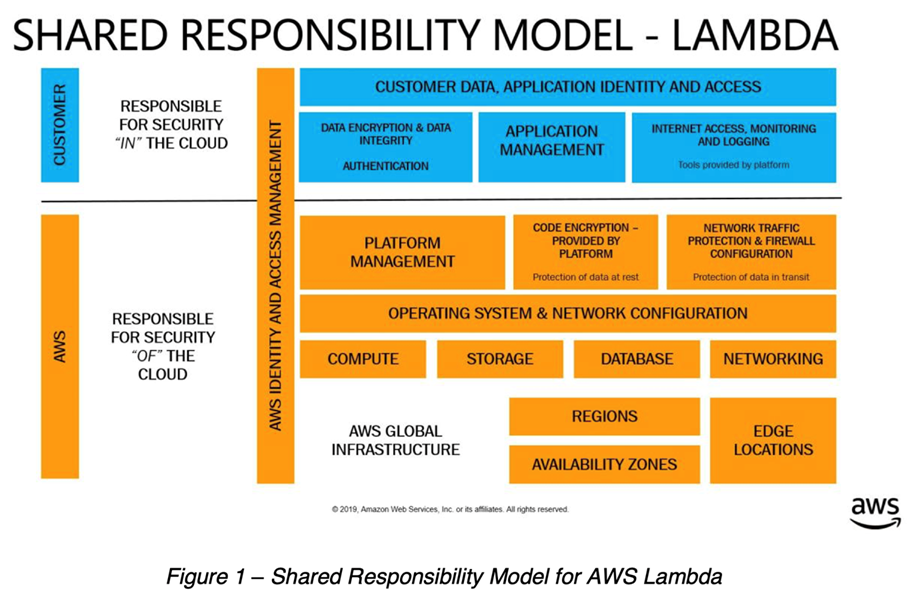
Unlike a traditional application running in the Cloud, with a serverless architecture AWS manages the underlying infrastructure, foundation services, virtualization layers, operating systems, and application platforms (see Shared Responsibility Model – Lambda) which significantly reduces risk surface and completely eliminates the largest attack vectors.
We also use several security oriented services from AWS to optimize our security posture, including:
- AWS Organizations (Hard separation of PROD / DEV / TEST resources at the AWS account level)
- AWS Secrets Manager
- AWS Config
- AWS Security Hub
Is MFA used?
Yes. MFA is mandatory for all AWS IAM user accounts, and we use the Virtual MFA device form factor for all users.
What password policies are set?
At present we are mirroring the recommendations from NIST (Section 5.1.1 – Memorized Secrets)
One exception is that we extend the minimum password length to 18 characters.
How do you separate data?
We use "AWS Organizations" which provides hard separation of PROD / DEV / TEST resources at the AWS account level.
More Information
For more information on Nuclei's security posture, please contact our network security team at security@nuclei.ai.

Comments
0 comments
Article is closed for comments.